How To Secure Your Smart Factory

Historically, reliability took precedence over security in the design of critical infrastructure, leaving many legacy networks without modern authentication protocols. As these older systems merge with cloud platforms and corporate IT, the potential for exploitation grows significantly.
Today, a breach not only risks data theft but can also lead to major disruption and substantial regulatory fines. Consequently, organizations must prioritize test and system development strategies that specifically address the unique vulnerabilities of operational technology, ensuring that new security layers do not interfere with the continuous nature of industrial processes.
The threat landscape is further complicated by a diverse array of actors, ranging from state-sponsored groups to those seeking industrial secrets. Since modern attacks often start in digital office networks before moving to the factory floor, siloed defense strategies are no longer effective. This convergence requires a unified approach to monitor the entire business environment. By integrating advanced detection tools into industrial manufacturing workflows, companies can bridge the technical gap between IT staff and engineers.
Cybersecurity: The Industrial Evolution's Backbone
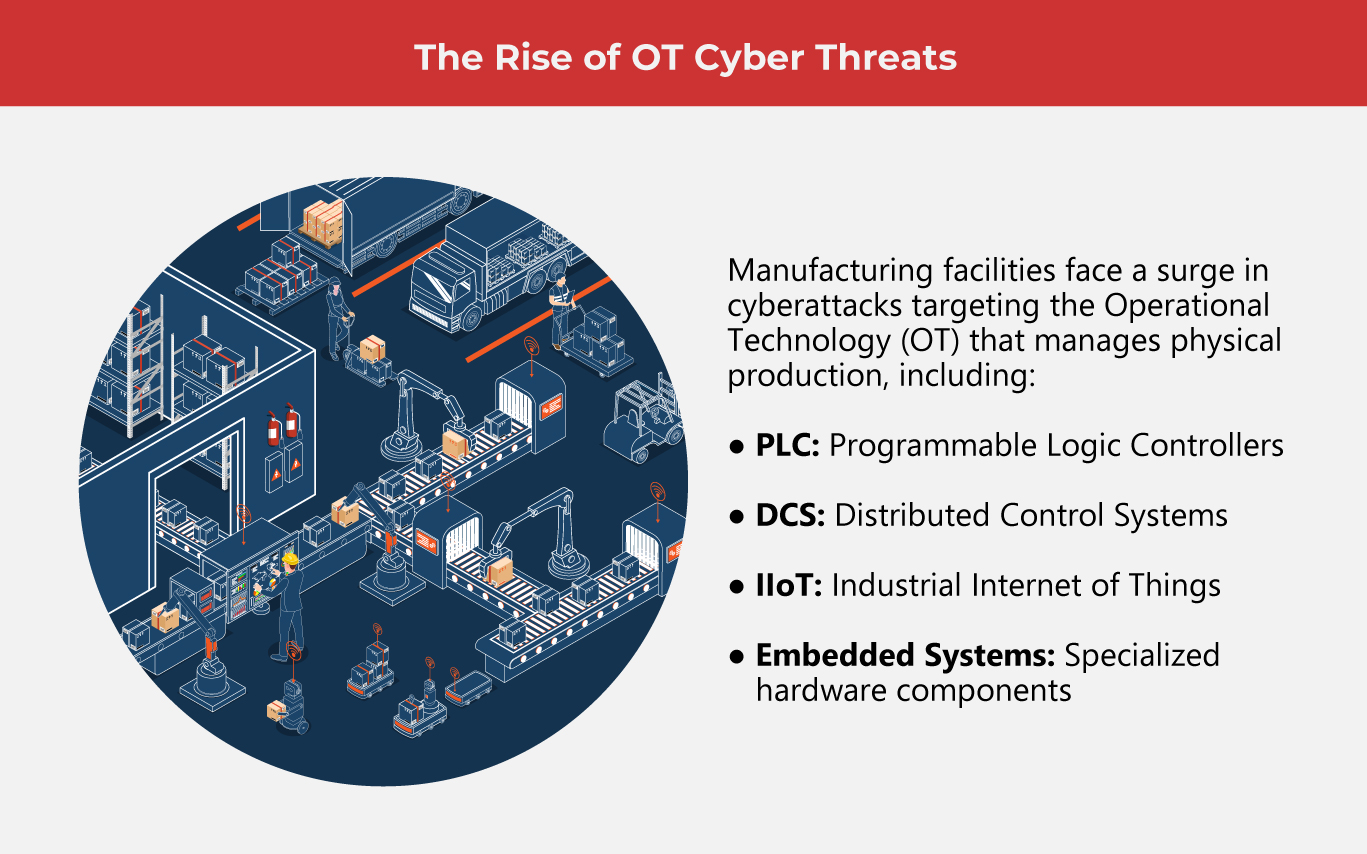
Industry 4.0 integrates AI and IoT to reshape the production landscape, yet this digital evolution introduces significant vulnerabilities. As factories transition to interconnected hubs, 48% of manufacturers now view cyberattacks as their primary operational risk. This connectivity exposes physical processes and sensitive intellectual property to sophisticated threats, making traditional defenses obsolete.
To maintain operational efficiency, modern facilities must adopt intelligent manufacturing solutions that bridge the gap between legacy hardware and new technology.
-
Active monitoring and risk identification
Modern industrial defense relies on constant visibility across Supervisory Control and Data Acquisition (SCADA) and Programmable Logic Controller (PLC) networks to catch anomalies preemptively. By integrating AI-driven analysis, advanced security software identifies subtle behavioral shifts that signal potential breaches, allowing operators to neutralize threats before they escalate.
-
Compartmentalization
Dividing operational technology from corporate IT networks is vital to prevent external breaches from reaching critical assets. By implementing firewalls and virtual LANs, organizations isolate essential systems. Testing solutions ensure these boundaries remain effective, stopping lateral movement and protecting industrial processes from digital threats.
-
Security patching
Many industrial security breaches stem from neglected vulnerabilities within controllers or Human-Machine Interface software. To remain future-ready, organizations must establish a disciplined maintenance cycle that validates and applies security patches without risking operational downtime.
-
High-security logins
To prevent unauthorized entry into sensitive control environments, organizations should prioritize multi-factor authentication and strict role-based access. By enforcing privileged account management and conducting regular permission reviews, teams can stop excessive permissions before they create a security gap. Incorporating these protocols into your reliability testing ensures that strict identity checks never compromise system integrity.
-
Crisis management
For global manufacturing leaders, maintaining a delicate balance between security and uptime is non-negotiable. Traditional IT response tactics, such as immediate system shutdowns, can cause catastrophic disruptions and financial losses in a production environment. Consequently, organizations must implement specialized response protocols that prioritize operational continuity, ensuring that threat containment strategies never compromise the critical flow of the supply chain.
(Also read: AI Can Improve Cybersecurity in 10 Ways)
5 Pillars of Smart Factory Cybersecurity
Achieving a secure smart factory requires seamless system integration to unify advanced threat detection with robust operational controls across the entire production floor.
-
Enhanced detection and analysis
Manufacturers must prioritize the deployment of advanced monitoring and diagnostic tools that deliver real-time alerts and high-fidelity insights. Successful system integration allows these technologies to bridge the gap between disparate network layers, providing a unified view of all data traffic and anomalies.
-
Cultivating a culture of vigilance
This step allows personnel to identify sophisticated threats like phishing before they penetrate the network. When secure behaviors are woven into the daily workflow, manufacturers significantly mitigate risks associated with it, ensuring that members contribute to the work environment’s integrity.
-
Upgrading defense systems
Deploying a sophisticated tech stack—including firewalls, encryption, and intrusion detection—creates a multi-layered shield around critical infrastructure. By integrating these protective measures, organizations can effectively harden their digital perimeter and ensure the resilience of their assets.
-
Assessing vulnerabilities
Organizations must move beyond reactive measures and adopt a policy of consistent vulnerability mapping. By quantifying the likelihood and potential impact of various digital risks, leaders can pinpoint exactly where their infrastructure is most exposed, letting them efficiently allocate resources.
-
Software upkeep
Maintaining digital hygiene through consistent software and firmware updates is a cornerstone of industrial defense. Because cybercriminals frequently exploit known vulnerabilities in aging code, manufacturers must prioritize a disciplined patching schedule that extends across both traditional IT systems and specialized OT or IIoT devices.
(Also read: How IIoT Powers Faster, Smarter Industrial Processes)
The Next Wave of Industrial Defense
Beyond foundational security, these emerging trends represent the next frontier of industrial resilience.
-
Autonomous AI defense
While machine learning optimizes production schedules and predicts equipment failures, it simultaneously introduces sophisticated new vulnerabilities. Forward-thinking manufacturers are now deploying advanced models to analyze vast data streams, allowing them to preemptively neutralize threats before they disrupt the production floor.
-
Strengthening the connected factory
The shift toward seamless data exchange across the IIoT streamlines operations but significantly broadens the digital attack surface. Securing these interconnected networks is now a baseline requirement to prevent unauthorized access and protect against the high costs of operational downtime.
-
Shielding the connected worker
Integrated sensors and wearable computing are revolutionizing workplace safety and proactive maintenance. However, as these devices collect sensitive data, manufacturers must prioritize encrypted data streams to ensure this personal information is never intercepted or manipulated.
-
Securing immersive environments
While virtual reality (VR) and augmented reality (AR) drive precision in design and maintenance through real-time simulations, their reliance on constant data exchange creates significant exposure. Protecting these immersive systems is vital to prevent hackers from compromising the integrity of digital blueprints or disrupting worker guidance.
-
Protecting high-volume data pipelines
Aggregating massive datasets allows for unprecedented process optimization and waste reduction, yet this centralized information becomes a high-value target for breaches. Securing data at rest and in transit ensures that the insights driving critical business decisions remain accurate and untainted.
-
Defending the 5G infrastructure
The shift to 5G provides the low-latency connectivity required for massive IoT deployments and real-time AI, but it also introduces numerous new entry points for cyberattacks. Implementing rigid security controls is necessary to safeguard the manufacturing floor as it becomes increasingly dependent on this high-speed bandwidth.
-
Aligning with regulatory frameworks
Adhering to updated standards like IEC 62443, NERC CIP, and ISO 27019 provides a proven roadmap for managing ICS risks. Following these global benchmarks ensures that security strategies stay consistent with the latest industry requirements and evolving legal expectations.
Securing the Future of Smart Production
The digital evolution of the factory floor has raised the stakes for industrial security to unprecedented levels. To thrive in 2026, manufacturers must transition from reactive patching to a proactive, multi-layered defense that prioritizes both operational uptime and data integrity. By committing to network segmentation, continuous monitoring, and specialized technical expertise, organizations can build the resilience necessary to lead in an era of total industrial connectivity. As one of the Top 30 EMS companies in the world, IMI has over 40 years of experience in providing electronics manufacturing and technology solutions.
As one of the Top 30 EMS companies in the world, IMI has over 40 years of experience in providing electronics manufacturing and technology solutions.
We are ready to support your business on a global scale.
Our proven technical expertise, worldwide reach, and vast experience in high-growth and emerging markets make us the ideal global manufacturing solutions partner.
Let's work together to build our future today.
Other Blog